This segment of the event logs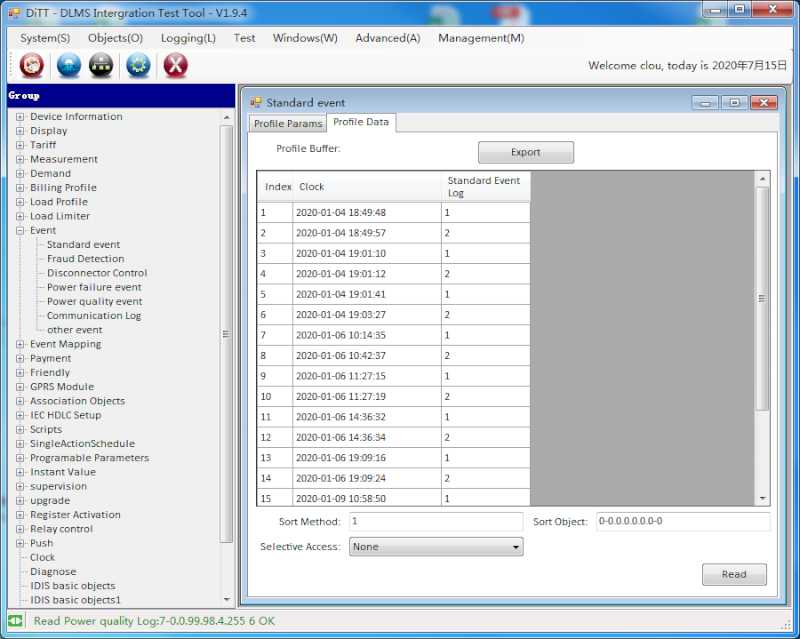 The Energy Meter Standard Event Log is capturing all possible meter manipulations and abnormal environmental conditions. Detecting tamper is one of my favourite subjects.
The Energy Meter Standard Event Log is capturing all possible meter manipulations and abnormal environmental conditions. Detecting tamper is one of my favourite subjects.
Like for the other log books we have for tamper events also an DLMS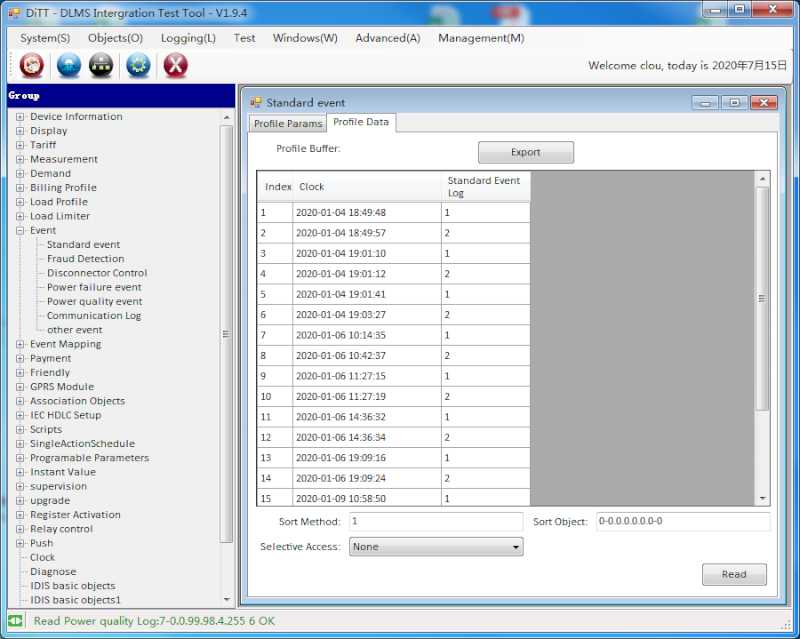 What is DLMS/COSEM ? OBIS code definition.
What is DLMS/COSEM ? OBIS code definition.
| Tamper event log | OBIS |
|---|---|
| Tamper event log, event object | 96.11.1.255 |
| Tamper event log | 99.98.1.255 |
You as utility staff know what a meter is capturing. My strong recommendation for the end users is: "Don't try to manipulate the meter."
Sometimes we receive comments like "Why is my meter in tamper mode?"
Actually the utility can tell you exactly, why. They simply look into the tamper log book and see what happened and when.
A small selection of possible tamper conditions
- Terminal cover removed
- Meter cover removed
- Communication module removed
- External meter box opened
- Strong magnetic DC field
- Current without voltage
- Voltage missing
- Unbalanced current in neutral
- Negative phase current
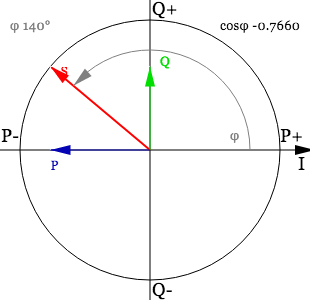 Negative Phase Current
Negative Phase Current - Bypass
- Reverse energy
- Low power-factor
- Neutral disturbance
- Failed authentication on optical port
 Security for Optical Ports on Energy Meters for several times
Security for Optical Ports on Energy Meters for several times - Decryption failure
- Replay attack
We can detect more, but we are not giving tampering guidelines. We assure that your utility revenue is protected and your losses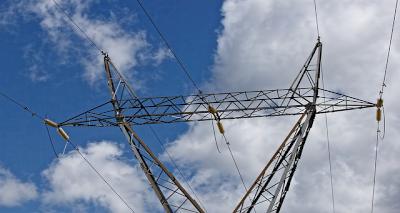 Technical vs Non-Technical Losses: What You Need to Know are minimized. Have a look at our AMI meters
Technical vs Non-Technical Losses: What You Need to Know are minimized. Have a look at our AMI meters Advanced Metering Infrastructure AMI and contact us
Advanced Metering Infrastructure AMI and contact us Contact Us for a more detailed discussion if you are interested in this topic. For certain reasons we will only reply on email addresses with utility domains.
Contact Us for a more detailed discussion if you are interested in this topic. For certain reasons we will only reply on email addresses with utility domains.
Final thoughts
We can not avoid tampering of energy meters. But we can detect it. Usually the utilities have set up a penalty catalogue to recover the cost.
We are continuously working on extended detection methods with and without external communication.

Detection of possible tamper for electromechanical meters need some more skills and experience. The meter installation on the photo looks at least suspicious. For such cases we have a nice tool. Have a look at our portable devices for on-site test Introducing Our High-Quality Meter Test Equipment for Precise Measurements.
Introducing Our High-Quality Meter Test Equipment for Precise Measurements.
Thank you for reading.
Editor's note: This article was originally published in July 2020 and has been updated for comprehensiveness.






Metre are always in tamper after two days
That's bad. The good thing is, by reading the tamper event log your power company can tell you why.
I got you from these explanations off course you can help my house from this darkness my meter no is 541508xxxxx and is in tamper mode this time help me with the codes pls
You need to ask your power company.
What if meter shows a padlock that is open
CLOU meters can show two padlocks. The padlock with outlines shows that the meter terminal cover was opened. The full black padlock shows that the meter cover was opened.
Unlock code if it shows black padlock
You need a clear tamper code. This code (token) can only be generated by your power supplier. It's an individual token based on your meter number and supply group code. It works only one time.