Nowadays, everything with a remote connection is declared to be smart, so most likely your TV too.
During the South African riots, it happened that the Samsung distribution centre in Cato Ridge (province KwaZulu-Natal) was robbed on July 11, 2021.
Stolen has been an unspecified number of Smart TVs.
On August 6th, Samsung announced that all of their TVs have an integrated TV Block function. So, the stolen TVs are remotely deactivated.
The company made clear that it can, at any time, remotely disable any and every Samsung TV connected to the internet. Most likely you've never heard about it.
The feature allows Samsung to check remotely whether TVs have been unduly activated and is already preloaded on all Samsung TV products.
The Technology
We don't know much. Samsung has only disclosed:
Once connected, the serial number of the television is identified on the Samsung server and the blocking system is implemented, disabling all the television functions.
First questions are arising regarding the privacy protection laws, especially in Europe.
My concern is, we don't know what else is implemented in smart devices. Samsung's case might only be the tip of the iceberg.
The server will definitely know your IP-address, location, usage-time, preferences and more. I wasn't able to find any statement about encryption. The function was hidden up to now.
Everything happens in the unprotected internet, so there are a lot of possibilities to cause harm to TV owners. The server can be hacked or spoofed, and suddenly you are disconnected. Or you are downloading a shiny 3rd party app on your TV which makes use of the blocking function. Later, you need to pay ransom to get your TV functions back.
More aspects you can find by reading the comments in the Samsung twitter account.
What is the difference to disconnection by smart meters?
The load switch inside of energy meters serves several functions like
a) additional protection for abnormal situations, e.g. over-voltage The Over- and Under Voltage Disconnection
The Over- and Under Voltage Disconnection
b) regional load control What is Load Shedding and How to Overcome?
What is Load Shedding and How to Overcome?
c) utility revenue protection
In case of tamper, the meter disconnects autonomous. The utility can read the meter log-file to know what happened and when.
The information is military grade encrypted and protected by unique keys. The authenticity of meter and server is verified by a key challenge. The key is never leaving the protected areas in meter and server. The IP-addresses are not public accessible.
All meters with DLMS logo are certified for communication security. The meter security part is here extremely simplified, but all security measures are traceable and transparent. The security standards are maintained by the DLMS association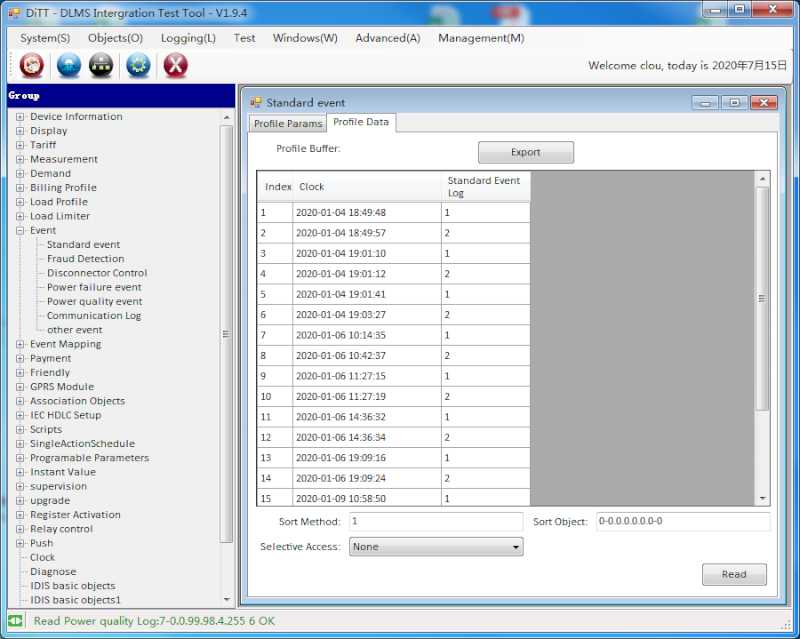 What is DLMS/COSEM ?.
What is DLMS/COSEM ?.
Conclusion
You need to be careful with all kind of IoT-Solutions, especially when they are not open standard. Don't download applications from unauthorized sources. Even Google Play had already issues with malware delivered on phones.
Beside of the established security solutions for advanced metering infrastructure Advanced Metering Infrastructure AMI, innovative IoT systems are coming up. Check not only the function, but also the security concept. Electrical power supply is a very critical piece of infrastructure.
Advanced Metering Infrastructure AMI, innovative IoT systems are coming up. Check not only the function, but also the security concept. Electrical power supply is a very critical piece of infrastructure.
Thank you for reading and stay safe.
Sources:
Computer Bild (in German language)
Samsung Newsroom South Africa
Editor's note: This article was originally published in August 2021 and has been updated for comprehensiveness.








All comments are moderated before being published. Inappropriate or off-topic comments may not be approved.